Vendor and Supplier Risk Management
Manage Third-Party Risk easily in vCIOToolbox
Protect your organization and brand from third-party risk with vCIOToolbox!
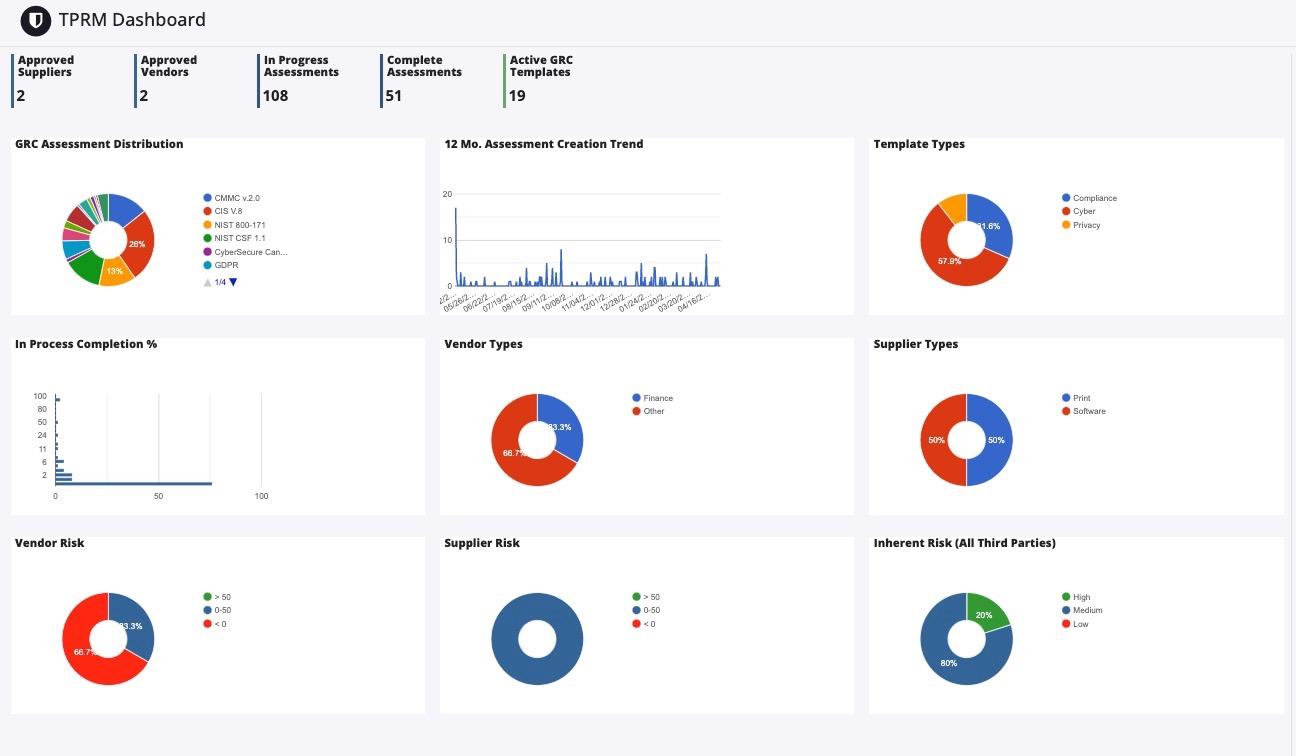
Our software platform provides organizations with the ability to proactively manage external risks posed by suppliers, contractors, partners and vendors. With tailored solutions for identifying potential threats in their various forms (cyber or business disruption), monitoring supplier performance, as well as ensuring effectiveness of controls – all within a single configurable solution – our tool helps companies reduce associated risks while optimizing operations across supply chains.
Understand the Impact of
Vendor Risk
Vendors can represent a direct risk to your business. The amount of due diligence you put into the relationship is directly related to how much inherent risk it carries, which includes its security practices, operations processes, and economic stability.
Residual risks are those that remain despite precautions taken on your end – these should be clearly understood before embracing a vendor partnership.
Significance to your Supply Chain
Evaluate how vital your vendor or supplier is to the success of your supply chain. Are they the only source you have access to? Such a situation can pose significant risks that must be addressed accordingly.
You’ll want to know whether confidential data such as PII and PHI are involved, so take appropriate steps toward establishing security controls if necessary.
It may prove beneficial for you to assess their geographic location. Certain areas could be susceptible to natural disasters and political unrest, making continued services difficult at best.
Assess Vendor Risk
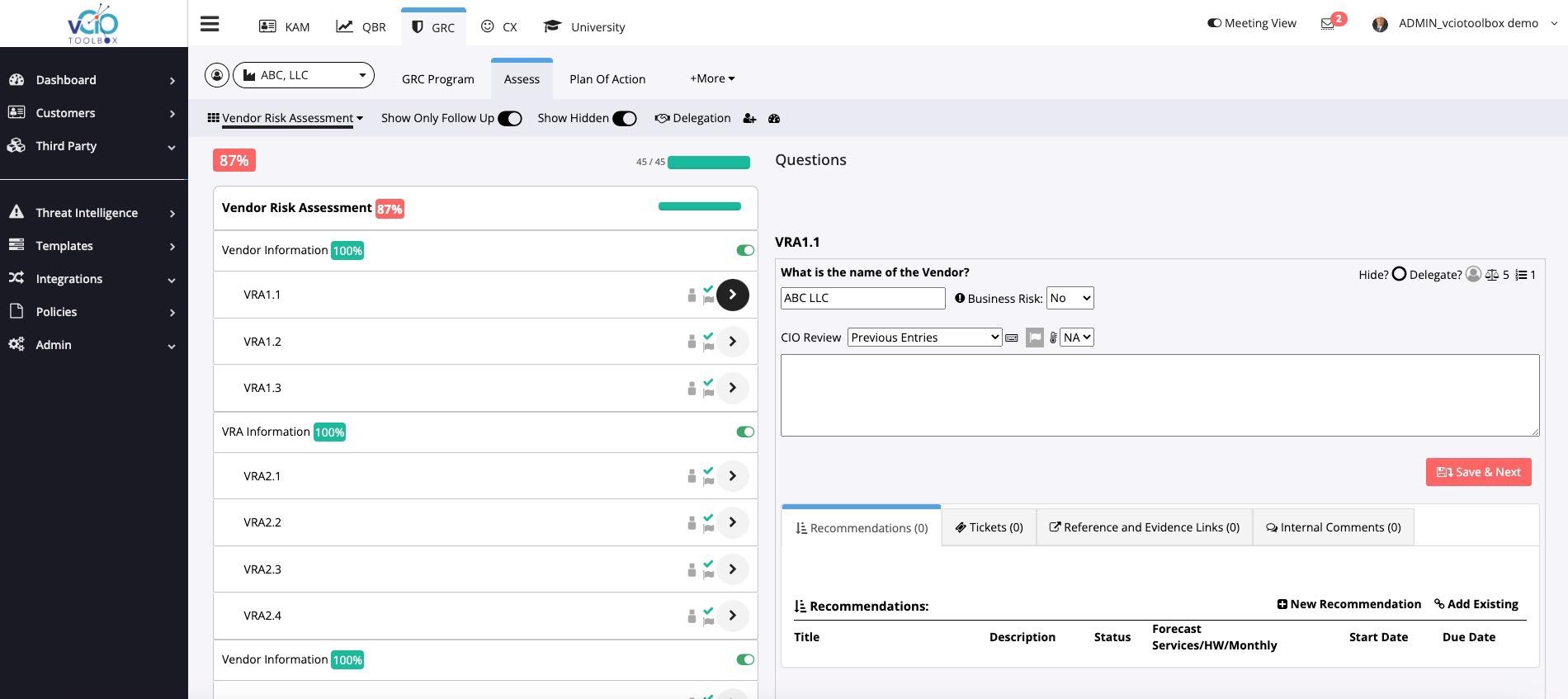
vCIOToolbox provides a comprehensive solution to quickly and easily launch vendor partnerships with pre-built questionnaires that you can share with your vendors and suppliers.
Leverage our Vendor Risk Assessment (VRA) or one of our standard frameworks, including NIST CSF, CIS v8, NIST 800-171, and GDPR, to support relationships in regulated industries.
Additionally, we make attaching evidence documents or policies simple and easy.
See the Full View of Each Vendor





Cybersecurity
Financial
Data Privacy
Operations
Compliance